
Retail Loss Prevention in 2026: Technology, Training, and Tactics
Organized retail crime is surging. We cover the detection strategies, technology tools, and staff training that help retailers protect their inventory.
Expert analysis on security threats, incident response strategies, and protecting your organization.

Organized retail crime is surging. We cover the detection strategies, technology tools, and staff training that help retailers protect their inventory.

A clear escalation framework that defines notification chains for different incident types and severity levels—from minor disturbances to critical emergencies.
A detailed checklist for evaluating physical security at any facility—perimeter, access control, lighting, surveillance, emergency systems, and operational procedures.

When a major incident happens at a client site, your response defines your reputation. This guide covers crisis planning, communication protocols, and recovery.

A thorough security audit identifies vulnerabilities before incidents occur. Use this comprehensive checklist to assess any facility's physical security posture.

When seconds count, guards need clear decision trees. This quick reference covers medical emergencies, fires, active threats, suspicious packages, and more.
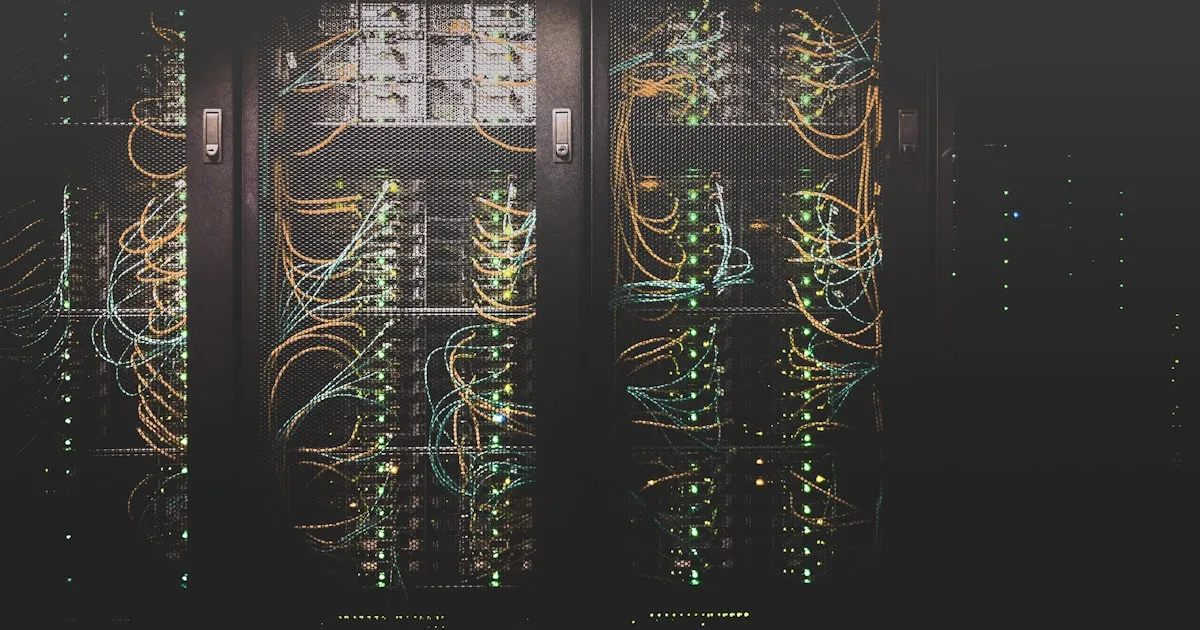
Data centers require the highest levels of physical security. This guide covers multi-layer access control, mantrap configurations, and 24/7 monitoring protocols.

Manufacturing facilities face threats from theft, industrial espionage, and workplace violence. This guide covers perimeter security, visitor management, and OSHA compliance.

With billions in inventory moving through warehouses, security is critical. This guide covers access control, surveillance placement, and cargo theft prevention.

Construction sites are high-value theft targets. This guide covers perimeter control, access management, equipment tracking, and safety protocols for securing active job sites.

Dispensaries face unique security challenges—cash-heavy operations, strict compliance requirements, and heightened theft risk. Here's how to protect them properly.

Gated communities, apartment complexes, and HOAs have unique security needs. Learn how to structure patrol services, access control, and resident communication.

A step-by-step framework for handling common security incidents—medical emergencies, trespassing, theft, and more. Includes downloadable checklists your team can customize.

School security requires a unique approach—balancing safety with a welcoming environment for students. This guide covers protocols, training, and technology.

Concerts, festivals, corporate events—each requires careful security planning. This guide covers staffing ratios, crowd management, and incident response protocols.

The Incident Command System isn't just for firefighters. Learn how security teams use ICS principles to coordinate complex incidents, from active threats to large-scale evacuations.

Hotel security must be effective yet unobtrusive. This guide covers lobby security, floor patrols, event security, and handling guest incidents professionally.

From risk assessment to emergency response, this guide covers how to protect congregations without creating a fortress atmosphere. Includes volunteer training tips.

Construction sites lose billions annually to theft. Mobile patrols, access control, and GPS-tracked equipment are changing how contractors protect their sites.

Healthcare security faces unique challenges—workplace violence, HIPAA compliance, psychiatric holds, infant abduction prevention. Here's how top hospital security teams operate.

You don't need an enterprise budget to build a functional SOC. This guide walks through the equipment, software, staffing, and processes needed for 24/7 monitoring.
Geofencing sounds simple, but poor configuration leads to constant noise or missed incidents. Learn how to set boundaries, buffer zones, and alert thresholds that actually work.

Security guards handle sensitive data every day—access logs, incident reports, visitor information. This primer covers the essential habits that protect that data from breaches.